
نظارات شمسية من CAPONI برؤية ليلية للرجال والنساء عدسات صفراء متغيرة بشكل ذكي نظارات طيران مستقطبة طراز UV400 BSYS3109|نظارات شمسية رجالية| - AliExpress

النظارات الصفراء النظارات الشمسية النظارات الشمسية للملابس النظارات الشمسية الصفراء, الجميلة, النظارات الشمسية للملابس, العدسات الصفراء التوضيح PNG وملف PSD للتحميل مجانا

سعر نظارات شمسية عصرية صفراء إطار صغير عدسات شفافة نظارات شمسية عتيقة شمسية إطار سداسي معدني ej فى الامارات | بواسطة امازون الامارات | كان بكام

نظارات للرجال النساء سيارات السائقين الرؤية الليلية نظارات شمس صفراء التوهج النظارات الشمسية القيادة نظارات: الشراء بأسعار منخفضة في متجر Joom الإلكتروني

لفيو نظارات رؤية ليلية ملفوفة، تناسب النظارات الطبية مع عدسات صفراء مستقطبة للقيادة الليلية, نظارة رؤية ليلية بإطار أسود/ عدسات صفراء A02, L: اشتري اون لاين بأفضل الاسعار في السعودية - سوق.كوم
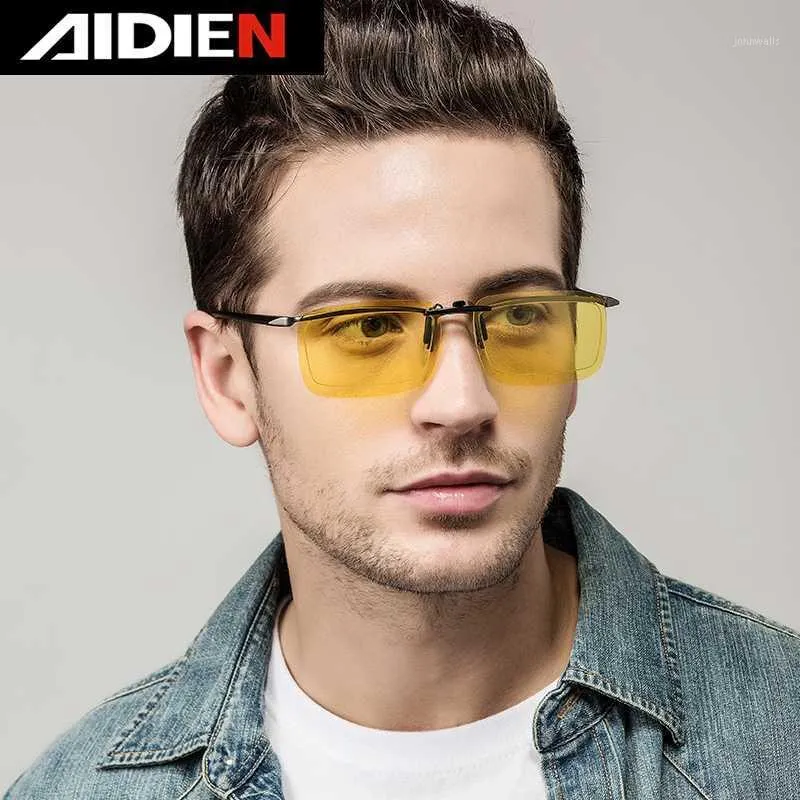
النظارات الشمسية الاستقطاب كليب على نظارات عدسة صفراء قصر النظر قرب الرجال النساء الرؤية الليلية المضادة وهج القيادة سيارة Goggle1 من 166.45ر.س | DHgate

نظارات شمسية صفراء عصرية للذهاب إلى الشاطئ, النظارات الحديثة, نظارة شمسيه, نظارات صفراء PNG والمتجهات للتحميل مجانا

نظارة افياتور بعدسات صفراء من نايت فيو، تحجب التوهج اثناء الليل ومناسبة لاي طقس - حماية 100% من الاشعة فوق البنفسجية الطويلة والمتوسطة - تٌقلل اجهاد العين وتسهل الرؤية اثناء للقيادة، قطعتين :

نظارات شمسية مستطيلة الشكل للرجال من جوبين، نظارات شمسية بإطار معدني من الألمونيوم والماغنسيوم لقائد الطيارات العسكرية، حماية من الأشعة فوق البنفسجية: اشتري اون لاين بأفضل الاسعار في السعودية - سوق.كوم الان













